Apple’s PassKeys update could make traditional passwords obsolete
Paul Haskell-Dowland, Edith Cowan University and Steven Furnell, University of Nottingham
Sometimes it seems like passwords have been with us forever, and yet every year we’re reminded how we still don’t use them properly!
The annual publication of the “worst passwords” list shows we haven’t become much more password savvy over the decade. And while several replacements for the humble password have been proposed, none have come close to the ease of using the traditional method.
But this changes today with the introduction of Passkeys – an update in Apple’s latest iOS 16 operating system. Passkeys could be the long-awaited solution to password malpractice, and the near-constant problem of compromised credentials.
What’s wrong with passwords?
The problem with passwords has been well documented. We choose weak ones, write them down (for others to see), share them, and re-use them on multiple websites.
The last of these is particularly problematic. Once your details are breached (and subsequently leaked), they’re vulnerable to “credential stuffing” – where cybercriminals take a set of login credentials and try them on multiple websites.
Author provided
“But I use a password manager,” you might say.
Well, that’s good. The standard advice for years has been to use password managers such as 1Password or LastPass. These let you create unique passwords for each website or service you use. So even if a website is compromised, only one password is revealed.
But this approach requires the ability to synchronise across all your devices – a feature not all password managers provide.
And even with a password manager, our passwords are still stored on the remote website we’re accessing. Although most websites store passwords in a secure (hashed) format, they are still routinely compromised. It’s estimated more than two billion sets of credentials (including passwords) were leaked online in 2021.
Along come Passkeys
Apple devices using the newest operating system release (iOS 16 or MacOS Ventura) will integrate a new password mechanism called Passkeys. Unfortunately iPad users will need to wait a little longer for the feature.
It’s worth noting you won’t be forced to use Passkeys, but your Apple device will prompt you with the opportunity to do so. Also, most websites will continue to support password access for people without the latest devices.
You’ll also have the option to use Apple’s secure cloud storage, iCloud, to back up your keys and share them across your Apple devices.
How do they work?
The concept behind Passkeys is relatively simple. Every website you elect to use Passkeys on will securely generate a unique pair of secret codes (referred to as “keys”).
One of these is a public key, stored on the website you’re registered on. The other is a private key stored on your device. Both keys are related, but one can’t be used to get the other.
When you attempt to log in to the website, instead of entering a password, your device will ask you to verify your login using your device’s biometric unlocking mechanism. So you’ll either scan your face or your finger.
This deliberately limits Passkeys’ functionality to devices with biometric support (iPhones have offered Touch ID since 2013 and Face ID since 2017).
Once your biometrics are verified, your device will use your private key to prove your identity to the website by tackling a complex mathematical “challenge” issued by the site. At no point is your private key sent across the internet to the website.
The response from your device can only be verified by the website, using the public key generated when you registered. And nobody can pretend to be you without your private key, which is safely stored on your device.
If a website is compromised, the public key alone is useless to cybercriminals.
Moreover, while biometric technology can be compromised, this is relatively difficult. To exploit a biometrics/PassKeys combination, a criminal would first need to obtain your device and then do a great job faking your face or fingerprint (or force one from you) – unlikely circumstances for most users.
Usability barriers
Passkeys will initially launch on Apple, but others are close behind. Microsoft will likely launch its own equivalent soon, although it may not initially be compatible with Apple’s implementation. This could be an issue for people wanting to use both an iPhone and Windows laptop.
Moving forward, it’s important Apple, Google and Microsoft work together to ensure maximum compatibility across devices.
Until then, there are some workarounds. If you need to access an Apple Passkeys-protected service on your Windows laptop (or any other device), you can scan a QR code with your iPhone and provide your biometric login verification that way.
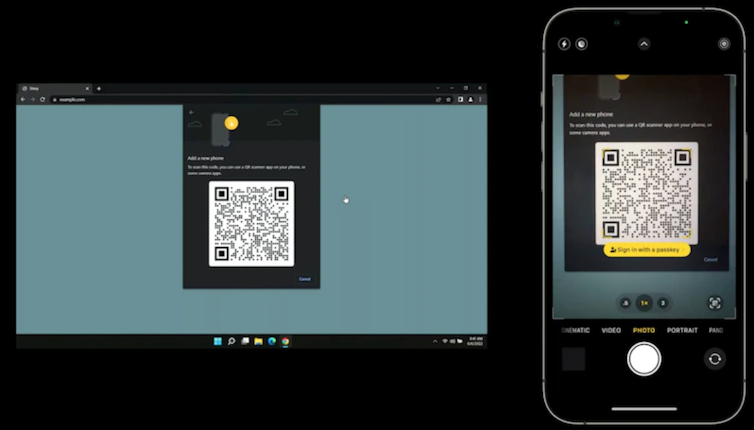
Apple
This means users will always need to have their phone on them when they want to authenticate to a remote service – whereas currently they can just type out their password, or use a password manager synced across their devices.
For some users, needing to have their phone all the time could be enough to give Passkeys a pass altogether.
The long tail of adoption
The Passkeys approach has the potential to make passwords obsolete, but this will require organisations around the world to invest time, effort and money into it.
Big players like social media companies are well positioned to adopt Passkeys early on, but there will be millions of websites that may take years to do so – or may never.
Indeed, looking at the state of play today, many leading sites still fall short of applying existing good practice around passwords. So it’s hard to say exactly how quickly, and how widely, Passkeys will be implemented.![]()
Paul Haskell-Dowland, Professor of Cyber Security Practice, Edith Cowan University and Steven Furnell, Professor of Cyber Security, University of Nottingham
This article is republished from The Conversation under a Creative Commons license. Read the original article.